Sharat is a Keynote Speaker, Startup Mentor, Emerging Tech Evangelist, and Ecosystem Builder. He advises across sectors, with a focus on blockchain, digital transformation, and fintech. Sharat is volunteering as the President of the Government Blockchain Association(GBA) India Chapter and is instrumental in driving engagements with Governments, Policy Makers, & Industry Associations.
“Who am I” might be a philosophical question; however, “Who are you” is an age-old question thrown at us at every conversation. Our identity is who we are and is a mechanism to bring trust to any interaction, whether physical or digital. With the widespread availability of the internet, digital identity is the most significant technological innovation. However, contrary to the rapid advancement of technology, there are over three billion people without a digital identity. Additionally, the authentication and online sharing of personal data models have hardly undergone any changes in the last few decades. Data leaks and unauthorized sharing of personal data have raised many security breaches costing billions to organizations. As per Gemalto, the world leader in digital security, 2.6 billion records were stolen, lost, or exposed worldwide in 2017, an 88% increase from 2016. Over the past five years, nearly 10 billion records have been lost, stolen, or exposed. An average of five million records compromised every day that accounts for 215,423 records every hour or 3,590 records every minute.
Identity Management
In the last four decades, the market has adopted different identity models to safeguard personal data. These models mostly fall under two categories – Centralized server or Federated Identity models. While in the Centralized model, we have a single database for storing users’ identities. In the Federated identity model as well, Identity Provider is the centralized database for all personal data. Hence, it’s the prime reason behind mass data hacks in the past, the second biggest reason being weak passwords. Both these issues primarily need to be addressed with the highest priority. In today’s world, the issuer, the data owner, and the verifier do not exist on a single network. Hence, the traditional mode of data sharing may lead to quite a few issues:
- The entire process is painfully time consuming and slow.
- The third-party has no direct way of knowing if the data is correct. Many organizations hire their independent background verifier team who reconnect with the issuer organization to cross-check the correctness of the data.
- The data is usually physical in nature, and the user often shares the photocopies of the data with the verifiers, even though part of the information is not needed by the latter.
- The issuer cannot revoke the certificate issued earlier, and even if he does, the verifier has no way to get updated.
- The data is not correlation-proof, and hence issuer who has information of many users can share it with other parties without informing the user, and third parties can use the information to trace back to the user
- High possibility of identity fraud and mismanagement of data
Hence, we need a new, improved process of data sharing that can handle the security, controllability, and portability aspects of data sharing with absolute ease.
Introducing Self Sovereign Identity
Over the past decade, different versions of distributed ledger technology (DLT) came to the market. The Self-Sovereign Identity (SSI) is the next-generation identity platform that leverages the benefits of DLT technology. With this new model, there would be no central repository of identity, and all individuals and organizations would be able to secure their personal data in their own privately owned wallet.
In the Self Sovereign digital identity model, personal data is stored in the user’s private digital wallet. The stored information is certified by issuers, which can be well-known organizations. The user can share all or selected data with the third-party verifier as per business need. The organization sends a reference to the Blockchain while issuing the certificate, which the verifier checks online to know if the data is valid. The issuer also can revoke a credential at a later point of time on the Blockchain in case the certified data expires after a certain period.
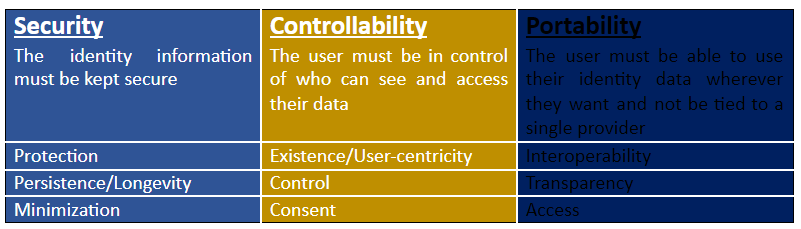
As per Self-sovereign identity (SSI) pioneer Christopher Allen, an efficient SSI network must follow the ten principles, creating a balance between transparency and fairness, and supporting the users within the system, and guaranteeing protection. The table below shows all the ten principles viz. user-centricity, control, access, transparency, longevity, portability, interoperability, consent, minimized data disclosure, and protection – categorized by security, controllability, and portability.
The New Wave: EarthId
EarthId has undertaken a mission of simplifying the identity management process to provide seamless access to online and offline services across industries. The team has developed an innovative Universal ID solution, which solves the critical problems with existing centralized and monolithic Identity Management Solutions cost-effectively and securely. This new solution alleviates the paramount issues of identity thefts and associated frauds, for both – individual users and institutions. The long-term vision of EarthId is to provide a self-sovereign digital identity to all human beings, thereby driving social and financial inclusion.
EarthId app available on both Android and iOS has the best solution to the existing problem with the binary identity system. EarthId is developed using Hashgraph, a 3rd generation distributed ledger platform, and state of the art cryptography technology to counter identity thefts and associated frauds. With the segregation of PII and transactional data, EarthId reduces the overall cost and complexity associated with the maintenance and validation of identities.
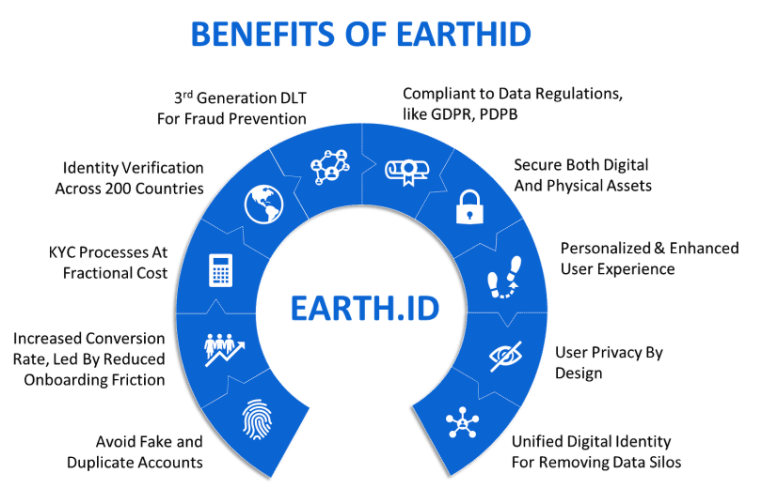
Powered by Hashgraph with its resistance to DDoS attacks, high scalability, and high throughput, EarthId fulfils the success criteria of an identity platform targeting 7.8 Billion people in the world. EarthId provides various integration mechanisms, including APIs, allowing organizations to integrate with their existing enterprise landscape and roll out its features to their global customer base seamlessly.






